By Justin Schorn, Senstar VP of Product Management
Adding a perimeter intrusion detection system (PIDS) to a site greatly increases its security and leverages the value of existing assets like security fences and surveillance systems.
With respect to types of systems available, site owners and system integrators have a wide variety of technologies to choose from – fence-mounted sensors, microwaves, active IR, and buried RF, to name a few.
In addition, given that many sites already have a surveillance system, video analytics may also be a cost-effective option.
Using reasonably priced HD and thermal cameras, security professionals can implement a wide range of video analytics to enhance security and obtain valuable business intelligence.
For example, video analytics can be used to define virtual fences, track people and objects, and perform face and license plate recognition.

While each technology has its own strengths, there can be substantial overlap in terms of capabilities and applications when it comes to dedicated PIDS sensors and video analytics.
Site owners, wanting to maximize their existing investments, may ask:
- “If I already have technology A, do I need B?”.
- For example, “if I have motion detection on my cameras, does a fence sensor increase my level of security?”
- Or, “if my gate is protected by a pair of microwaves, will video analytics applied to a camera’s video stream add any extra value?”
When it comes to video analytics and PIDS, there is no one size fits all solution.
This article looks at best practices when integrating video analytics with PIDS and offers approaches that can assist in meeting a site’s security, operational and budgetary requirements.
(Learn More about Symphony, the new benchmark for intelligent video management software (VMS). Highly scalable, easy to set up and use, Symphony is the perfect solution for both single server installations and multi-server deployments. Courtesy of Senstar and YouTube. Posted on Sep 26, 2017)
Protecting Perimeter Fences
The most common approach to protecting perimeter fences is to use fence-mounted sensors.
Consisting of a coaxial cable, fiber optic cable, or set of accelerometers attached directly to the fence, fence-mounted sensors detect any attempt to cut, climb, or lift the fence fabric.
Modern systems use a variety of sensing techniques (time-domain reflectometry or accelerometers, for example) and provide highly useful features like environmental compensation, precision ranging, cut immunity, and low-voltage power over sensor cables.
These systems work well and are generally easy to install along the entire length of the perimeter.

Fences may also be protected by other sensors, such as active IR or buried RF.
While very different technologies, both are used to generate invisible detection walls or fields, typically on the inside of the perimeter.
Active IR is low cost but only works in straight lines, while buried RF requires a clear area with good drainage.
Being installed on the protected side of the perimeter means that when an alarm does occur, the likelihood of the event being a legitimate security concern is very high.
Intelligent lighting with integrated intrusion detection capabilities is new in the security market.
(Learn More. The Senstar LM100 is the world’s first intelligent perimeter lighting and sensing solution which combines high performance LED lighting with accelerometer-based sensors, the LM100 acts as powerful deterrents against intruders, detecting and illuminating them at the fence line while alerting a security management system (SMS). Courtesy of Senstar and YouTube. Posted on Sep 26, 2017)
Installed on the fence, LED-based luminaires provide uniform, wide-spectrum illumination targeted along the fence line while embedded accelerometers detect any attempts to breach the fence.
In addition to having similar advantages to those of other fence-mounted sensors, intelligent lighting enhances the video quality of the cameras and acts as an immediate deterrent by illuminating the fence whenever an intrusion attempt is detected.
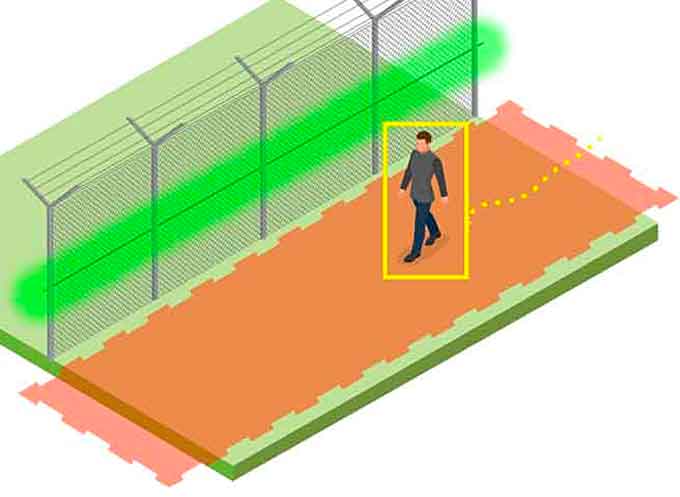
Intrusion attempts can also be detected via video analytics by using either virtual tripwires defined along the fence or area masks.
Entry-level analytics use simple motion detection while more advanced analytics use sophisticated algorithms that detect and classify the presence of people, vehicles, and objects.
There are several benefits to using the site’s surveillance system for intrusion detection:
- The same cameras can be used for detection and assessment capabilities
- The per-video stream analytic cost is very low, and
- Detection is not limited to just the fence (i.e. the systems can detect and potentially track individuals both inside and outside the perimeter)

However, if the implementation of video analytics is to be successful (that is, provide a high probability of detection while minimizing nuisance alarms), the following rule must be observed: video analytics work only as well as the quality and coverage of their video streams.
This means that:
- For perimeter intrusion detection applications, fixed cameras must have line of sight visibility of the entire fence line.
- Cameras must be installed in such a way to avoid movement and vibrations caused by wind.
- The cameras must be able to provide clear images under low light situations. Weather conditions including snow, rain and dense fog will affect visibility and detection capabilities.
- Video analytics typically require buffer space around the detection area that may be impractical in busy environments, such as urban areas with adjacent sidewalks.
- The algorithms must be optimized for outdoor use and be able to distinguish between people/objects of interest and background noise like shadows or vegetation movement.
These practical considerations do not diminish the power of video analytics.

On the contrary, when properly deployed and integrated, video analytics offer an exciting new set of capabilities that greatly enhance perimeter security at relatively low cost:
- Supplement fence sensors by providing additional detection capabilities (especially important for low fences, ornamental fences, and walls)
- Determine the direction of intrusions (ingress or egress)
- Provide covert detection (no visible equipment on fence)
- Detect and track people near both sides of the perimeter fences to provide early warning of potential security events before they can occur.
- This early warning can be used to direct PTZ cameras, so that high-resolution video can be captured of the intruder at the time the alarm (from the fence sensor) is generated
- Use anti-loitering analytics to detect persons “camped out” near the perimeter
- Track intruders with a PTZ camera after an alarm is generated (assists in assessment, response, and evidence collection).

Protecting Gates
Balancing the operational and security requirements of actively used gates calls for careful attention.
A successful implementation needs to take into account authorized traffic, hours of operation, and the construction of the gate itself.
For swinging gates, a fence-mounted sensor can be installed on each moving panel.
- If the sensor is cable-based, the cable is looped around the fabric and routed underneath the gate to the other side.
- With this setup, the sensor can detect intrusions whenever the gate is closed.
- To enable authorized entry, the sensor could be masked during business hours or temporarily disabled via a keypad or another access control system.

Sliding gates have always posed a problem for cable-based sensors.
- Traditionally, a mechanical cable retraction system is used to manage the routing of the sensor cable from the fence to the sliding gate panel.
- These systems are expensive, cumbersome, and prone to failure.
One common solution is to protect the gate with a pair of microwave or active IR sensors.
- Placed immediately behind the gate, they can detect intruders upon entry (either after breaching the gate if closed or simply walking in if open).
- This setup can work quite well, although it requires the installation of additional equipment.
Another solution is to use a wireless gate sensor.
- An embedded accelerometer analyzes gate movement in three-dimensions, enabling the sensor to distinguish between gate activity, intrusion attempts, and environmental conditions.
- The sensor communicates with a nearby processor over an encrypted and monitored wireless link.
- If any suspicious event occurs – intrusion attempt, communication link failure, or an attempt to remove the sensor from the gate – an alarm is immediately generated.
(For instance, the FlexZone Wireless Gate Sensor is an accelerometer based intrusion detection sensor that detects attempts to open, cut, climb, or otherwise break through a sliding or swinging gate. The sensor module is attached directly to the gate panel with tie-wraps and communicates with a nearby receiver card (installed in a FlexZone processor) over an encrypted wireless link. Courtesy of Senstar and YouTube)
Video analytics can play an important role with gate protection, both in terms of improving security and operational efficiency.
Most sites already have fixed cameras that monitor gate activity.
Applying analytics to the video stream provides an impressive set of additional capabilities:
- Intrusion detection analytics can be used to enhance after-hours detection (either tripwires or area masks), especially with low gates or rising arm barriers.
- Video analytics can also work to detect secondary intrusions or tailgating (for example, someone entering through the gate when a vehicle is stopped between a pair of microwaves).
- License plate recognition can be used to both track all vehicles in and out of the site. In addition, known (authorized) plates could trigger rules that automatically open the gate or temporary bypass the gate sensor.
- Face recognition analytics can be used to temporary disable alarms for authorized users or alarm upon unauthorized person detection.
- Vehicle/people tracking analytics can count the number of in/out vehicles or people.
Site-Wide, Integrated Security
The enhanced detection and assessment capabilities provided by the integration of PIDS with video analytics are very exciting, but system integrators must keep in mind that these can only be fully realized if the devices and management software work together.
The key to a successful integration is selecting equipment and software that support open interfaces, enable rules and logic to be applied to the data, and integrating the relevant data into a cohesive operator interface.
About the Author:

Justin Schorn is the VP of Product Management at Senstar Corporation, where he oversees the strategic development of video management and perimeter intrusion detection products.
Justin was a co-founder of Aimetis Corporation, a world-leader in the fields of video management and analytics, which amalgamated with Senstar in 2016.
He previously worked at DALSA, a global leader in digital imaging. Justin graduated from the University of Western Ontario with an Honors degree in Political Science.
Learn More…
Multiple Senstar Systems Chosen to Protect Major US Airport (Multi-Video)
















