
Guest editorial by Petko Soyanov, Global CTO of Forcepoint
Late last year, Chinese researchers claimed to use quantum computing to break an RSA public-key encryption algorithm.
While many quantum experts expressed skepticism, the announcement points up a chilling fact: Within the next decade, there’s a strong possibility quantum computers will break common encryption codes.
Does your organization need to worry about a cyberattack ten years in the future?

The short answer is yes.
Any data you’ve adequately encrypted today is currently safe from being read by unauthorized users.
But a motivated cybercriminal could steal your data now and simply hold onto it till quantum computing catches up with existing cryptography.
At that point, your sensitive data could be exposed.
Fortunately, there are strategies and technologies you can deploy right now to reduce your attack surface and minimize today’s risk of tomorrow’s hacks.
Race to Post-Quantum Cryptography
For certain use cases, quantum computers promise to be exponentially faster than classical computers. Classical computers encode data as bits, which can have a value of 0 or 1.
Quantum computers encode data as quantum bits, or qubits, which can have a value of 0, 1, or a combination of the two.

Quantum computers could revolutionize logistics planning, drug discovery, weather forecasting, and more. But they’ll also be good at breaking encryption codes.
Just how good? Where a classical supercomputer would need hundreds of years to crack an RSA 256 code, a quantum computer will complete the task in a day.
That means existing encryption algorithms will need to be updated. But the news isn’t all grim.
First, only public-key cryptography – used to protect financial transactions and digital signatures, for instance – will need to be replaced. If your data is protected with AES 256 symmetric cryptography, you’ll just need to upgrade to longer keys.
That is, unless your AES cypher was established using a public key, in which case you’ll need to replace it.
Second, IT vendors have been developing stronger “post-quantum” algorithms. The National Institute of Standards and Technology (NIST) plans to publish post-quantum encryption standards next year.
Still, the target date for organizations to complete the implementation of quantum-resistant cryptography isn’t till 2035.
In the meantime, here are five actions you can take to protect your data now:
-
Deploy strong cryptography.
Your organization will need to upgrade or replace its encryption before quantum computers can crack codes. But in the meantime, make sure you’re using the strongest encryption currently available, such as AES 256.
Some organizations still rely on older encryption algorithms already known to be hackable. And many enterprises have no idea what encryption technology they’re using.
Assign someone in your IT organization to assess your encryption solutions and those of your vendors.
-
Identify sensitive information and assess the risks associated with storing it.
Data can be your organization’s greatest asset. It can also be a major liability.
Last fall, the hack of an Australian telecom company exposed one in three of the nation’s citizens to identity fraud.
The breach was so severe in part because the company retained extensive customer personal identifiable information (PII), including passport and driver’s license numbers – in some cases, even for past customers.
(Up to 9 million past and present Optus customers have been hit by one of the biggest cyber attacks in Australian history. That’s nearly 1 in 3 people across the country with the company now racing to contain the fallout. The big banks have been alerted, and Australia’s international spy network is working to hunt down the culprits. Optus says the hackers may have a customer’s name, date of birth, phone number, and email address. For some, their home address, driver’s licence, and passport number too. Courtesy of 7NEWS Australia and YouTube. Posted on Sep 22, 2022.)
To reduce this kind of risk, take a thorough inventory of your customer, employee, and intellectual property (IP) data.
Document where it’s stored – in your data center, in cloud storage services, on user devices, in email messages – and who has access to it.
Then work with your governance, risk, and compliance function to determine the risk of retaining all that data.
-
Implement data-retention policies to reduce your data attack surface.
Many organizations lack clear policies for how long they retain information.
In part, that’s because finance, legal, compliance, engineering, and other functions all have different data-retention needs. The result is an ever-growing data attack surface.
You need a structure for the classes of data you own and how long you should store each type.
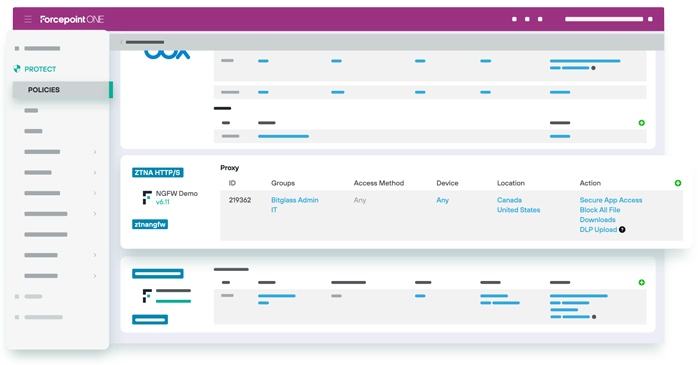
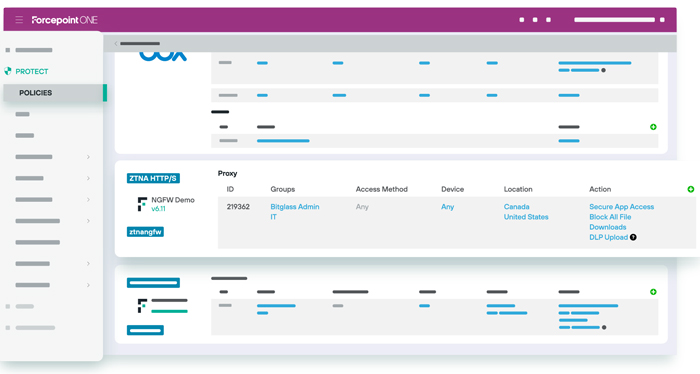
Zero Trust access to cloud applications with continuous control of business-critical data, no matter where users are or what device they use.
Classify data by its sensitivity, its risk of exposure, and the impact of exposure. Then set guidelines for how long to keep each type of data based on regulatory requirements.
Also, consider how you store information. For instance, if you don’t require regular access, consider storing data on backup media that’s isolated from external networks.
Finally, spell out processes for deleting information at the end of the retention period. And for all these efforts, involve stakeholders across functions to be sure retention policies meet internal needs.
-
Implement data controls beyond encryption.
No organization should rely solely on encryption to protect data. You need a more holistic, layered approach.
Start with access controls such as multifactor authentication (MFA). MFA combines something a user knows (a password), something the user has (a device), and something the user is (biometrics).
Simple, safe, and scalable Zero Trust remote access to internal and private cloud applications – without a VPN.
Even stronger MFA adds an external element, such as a code sent to a smartphone.
Strategies like data tokenization and anonymization can further protect data. Tokenization substitutes sensitive data elements with tokens that have no meaning out of context.
The token maps back to the original data element, but without the tokenization systems, bad actors would have a very hard time re-creating the data.
Finally, implement zero trust network access (ZTNA). With ZTNA, all entities – including users, devices, and applications – that want access to your data must authenticate their identity, every time they ask for access. That helps prevents cyberattacks from spreading laterally throughout your networks.
(It’s no secret that much of the world’s malware and ransomware makes its way to organizations through infected files. This overview video explains how Zero Trust Content Disarm and Reconstruction (CDR) strips malware from office documents, images and PDFs. Put an end to Zero Day malware with Forcepoint Zero Trust CDR. Courtesy of Forcepoint and YouTube.)
-
Continuously scan systems for new data that needs protection.
Your data is a continually expanding resource, so you need to constantly update your view of it.
Several vital cybersecurity solutions can help.
Data loss prevention (DLP) is a set of technologies designed to identify, classify, monitor, and protect data.
These tools scan your networks, email, endpoints, and other IT resources to track which devices and software people use to access your data, how they share that information, and whether they’re following data usage policies.
(Learn more about Forcepoint Data Loss Prevention. Courtesy of Forcepoint and YouTube.)
A cloud access security broker (CASB) enables similar visibility in the cloud.
Sitting between your users and your cloud service provider, a CASB lets you identify and monitor the use of cloud apps. It can uncover high-risk behavior and enforce policies and controls to protect sensitive data.
An arms race is emerging as nations vie to be the first to develop viable quantum computers.
There will likewise be a race between hackers who use quantum technology break encryption codes and enterprises rushing to replace their encryption protections.
Don’t allow your organization to be caught short. Take action now to assess your encryption solutions and establish a plan for upgrading to post-quantum technology as it becomes available.
Simultaneously, deploy proven cyber strategies and technologies that will protect your data now and in the future.
About the Author

Petko Soyanov is Global CTO of Forcepoint, a provider of comprehensive, cloud-native cybersecurity solutions.
He focuses on strategy, technology, innovation, and go-to-market activities across Forcepoint’s solution portfolio, with specialties in enterprise security engineering, threat intelligence, incident response, enterprise encryption, and cross-domain solutions.
Mr. Soyanov is also co-host of the To the Point Cybersecurity Podcast, a member of the ATO on AWS Advisory Board, and a STAR mentor for MACH37 Cyber Accelerator.
Previously Mr. Soyanov held leadership roles at a variety of high-tech and public-sector organizations.
Forcepoint is a global leader in data-first cybersecurity.
 The company’s behavior-based solutions adapt to risk in real-time and are delivered through a cloud-native SASE security platform that protects users, devices, and networks as people access the web and cloud, prevents the theft or loss of sensitive data and intellectual property no matter where people are working, and eliminates breaches caused by insiders.
The company’s behavior-based solutions adapt to risk in real-time and are delivered through a cloud-native SASE security platform that protects users, devices, and networks as people access the web and cloud, prevents the theft or loss of sensitive data and intellectual property no matter where people are working, and eliminates breaches caused by insiders.
Forcepoint, based in Austin, Texas, creates safe, trusted environments for thousands of enterprise and government customers and their employees in more than 150 countries.
To learn more, please visit www.forcepoint.com.
Forcepoint Nominated in 2023 ‘ASTORS’ Homeland Security Awards Program

American Security Today’s Annual ‘ASTORS’ Awards is the preeminent U.S. Homeland Security Awards Program, and now entering its Eighth Year, continues to recognize industry leaders of Physical and Border Security, Cybersecurity, Emergency Preparedness – Management and Response, Law Enforcement, First Responders, as well as federal, state and municipal government agencies in the acknowledgment of their outstanding efforts to Keep our Nation Secure.
Forcepoint
Best Phishing Defense Solutions
-
Zero Trust Content Disarm and Reconstruction
-
Forcepoint is leading the shift from outdated and ineffective malware and ransomware detection strategies to a proven prevention strategy rooted in Zero Trust principles.
-
With its Zero Trust Content, Disarm, and Reconstruction (ZT CDR) solution, Forcepoint gives IT and security teams a fresh new way to proactively protect their organization from ever-increasing malware and ransomware threats.
-
Forcepoint ZT CDR differentiates itself from traditional security inspection solutions by, instead of trying to detect the presence of malware; it assumes nothing can be trusted. It extracts only valid business information from files – either discarding or storing the originals and any malware they might contain – and then builds brand new, fully functional files to carry the information to its destination.
-
Pivoting from detection to prevention in this way is especially important with the recent evolution in hybrid workforces and digital transformation, and their resultant usage of content and electronic information everywhere.
-
By leveraging a data-first approach to malware threat removal, ZT CDR is revolutionary for mitigating the threat of compromised data that could lead to breaches.
(It’s no secret that much of the world’s malware and ransomware makes its way to organizations through infected files. See briefly how Zero Trust Content Disarm and Reconstruction (CDR) strips malware from office documents, images, and PDFs to put an end to Zero Day malware. Courtesy of Forcepoint and YouTube.)
-
*Forcepoint was also a recognized in the 2021, 2019, and 2018 ‘ASTORS’ Homeland Security Awards Programs respectively.
The continually evolving ‘ASTORS’ Awards Program will highlight the trail of Accomplished Women in Leadership in 2023 and the Significance and Positive Impact of Advancing Diversity and Inclusion in our Next Generation of Government and Industry Leaders. #MentorshipMatters
So be on the lookout for exciting upcoming announcements of Speakers, Presenters, Book Signing Opportunities, and Attendees at the 2023 ‘ASTORS’ Awards Presentation Luncheon in November of 2023 in New York City!
Nominations are currently being accepted for the 2023 ‘ASTORS’ Homeland Security Awards at https://americansecuritytoday.com/ast-awards/.
Comprehensive List of Categories Include:
| Access Control/ Identification | Personal/Protective Equipment | Law Enforcement Counter Terrorism |
| Perimeter Barrier/ Deterrent System | Interagency Interdiction Operation | Cloud Computing/Storage Solution |
| Facial/IRIS Recognition | Body Worn Video Product | Cyber Security |
| Video Surveillance/VMS | Mobile Technology | Anti-Malware |
| Audio Analytics | Disaster Preparedness | ID Management |
| Thermal/Infrared Camera | Mass Notification System | Fire & Safety |
| Metal/Weapon Detection | Rescue Operations | Critical Infrastructure |
| License Plate Recognition | Detection Products | COVID Innovations |
| Workforce Management | Government Security Programs | And Many Others to Choose From! |
Don’t see a Direct Hit for your Product, Agency or Organization?
Submit your category recommendation for consideration to Michael Madsen, AST Publisher, at: mmadsen@americansecuritytoday.com.
Homeland Security remains at the forefront of our national conversation as we experience an immigration crisis along our southern border and crime rates that are dramatically higher than before the Pandemic across the United States.

These challenges have become a national priority with an influx of investments in innovative new technologies and systems.
Enter American Security Today, the #1 publication and media platform in the Government Security and Homeland Security fields, with a circulation of over 75,000 readers and many tens of thousands more who visit our AST website at www.americansecuritytoday.com each month.
The pinnacle of the Annual ‘ASTORS’ Awards Program is the Annual ‘ASTORS’ Awards Ceremony Luncheon Banquet, an exclusive, full-course plated meal event, in the heart of New York City.

The 2022 exclusive sold-out ‘ASTORS’ luncheon featured representatives of law enforcement, public safety, and industry leaders who came together to honor the selfless service of those who stand on the front lines and those who stand beside them – providing the capabilities and technologies to create a safer world for generations to come.
Last year marked the 20th anniversary of the Department of Homeland Security (DHS), which came out in force to discuss comprehensive collaborations between private and public sectors that have led to the development of intelligence and technologies which serve to protect our nation.

The keynote address was provided by U.S. Customs and Border Protection (CBP) Office of Field Operations (OFO) Deputy Executive Assistant Commissioner (DEAC) Diane Sabatino, who described the changes to CBP through the tragedy of 9/11 and the relentless commitment to its mission and ongoing investment in the latest technologies and innovations to protect our borders and Homeland.
The resounding theme of the DEAC’s remarks was her pride in the women and men of the CBP and their families who support them.

AST was also joined by Legendary Police Commissioner William Bratton, who spoke about his love for the City of New York, the Profession of law enforcement to which he has dedicated his life, and for which he continues to drive thought leadership and innovation.
New York City Police Department (NYPD) Chief of Department Kenneth Corey, came out to address Luncheon attendees and shared some of his experiences and the changes in policing he’s witnessed over his more than three decades of service.

FDNY Chief Joseph Jardin honored the men and women of the FDNY, not only those who currently serve but all of those who have selflessly served, with special recognition of those lost on 9/11.
Chief Jardin spoke about the continuing health battle of many following 9/11 with cancer and respiratory disease, yet now knowing the full consequences, would not have made a different decision to respond.
As Chief Jardin noted, mission-driven service is the lifeblood of every firefighter, volunteer, and sworn member, and has been so throughout the history of the Fire Service.
Former head of the FBI’s active shooter program, Katherine Schweit joined AST to sign complimentary copies of her book, ‘STOP THE KILLING: How to End the Mass Shooting Crisis,’ thanks to the generosity of our 2022 ‘ASTORS’ Awards Sponsors.
The 2022 ‘ASTORS’ Awards Program was Proudly Sponsored by NEC National Security Systems (NSS), ATI Systems, Automatic Systems of America, guardDog AI, Fortior Solutions, IPVideo Corporation, Rajant Corporation, RX Global, and SIMS Software!
We were pleased to welcome the esteemed New York City Fire Department (FDNY); the New York City Police Department (NYPD); and the NYC Hospital Police, as well as Executive Management from the U.S. Cybersecurity and Infrastructure Security Agency (CISA), and many other DHS agencies, Federal law enforcement agencies, and private/public partnerships such as the National Association of Women Law Enforcement Executives (NAWLEE), the 30×30 Initiative, a coalition of professionals advancing the representation of women in policing; and Operation Lifesaver, Inc. (OLI) (rail safety advocates).

The prestigious Annual ‘ASTORS’ Homeland Security Awards Program highlights the most cutting-edge and forward-thinking security solutions coming onto the market today, to ensure our readers have the information they need to stay ahead of the competition and keep our Nation safe – one facility, street, and city at a time.

In 2022 over 240 distinguished guests representing Federal, State, and Local Governments, and Industry Leading Corporate Firms gathered from across North America, Europe, and the Middle East to be honored among their peers in their respective fields.
Each year, to keep our communities safe and secure, security dealers, installers, integrators, and consultants, along with corporate, government, and law enforcement/first responder practitioners, convene in New York City to network, learn and evaluate the latest technologies and solutions from premier exhibiting brands at ISC East, the Natural Disaster & Emergency Management Expo (NDEM EXPO), and the ASIS NYC Expo.
ISC East is the Northeast’s leading security & public safety event, hosted in collaboration with sponsor Security Industry Association (SIA) and in partnership with ASIS NYC.

 Corporate firms, the majority of which return year to year to build upon their Legacy of Wins, include:
Corporate firms, the majority of which return year to year to build upon their Legacy of Wins, include:
Advanced Detection Technologies, AMAROK, ATI Systems, Axis Communications, Automatic Systems, BriefCam, Canon U.S.A., Cellbusters, CornellCookson, CyberArk Fortior Solutions, guardDog.ai, Hanwha Techwin of America, High Rise Escape Systems, IPVideo Corporation, Konica Minolta Business Solutions, NEC National Security Systems, NICE Public Safety, OnSolve, PureTech Systems, Quantum Corporation, Rave Mobile Safety, Regroup Mass Notification, Robotic Assistance Devices, Rajant Corporation, SafeLogic, Select Engineering Services LLC, Singlewire Software, SolarWinds Worldwide, Teledyne FLIR, Valor Systems, and West Virginia American Access Control Systems, just to name a few!
Why American Security Today?
The traditional security marketplace has long been covered by a host of publications putting forward the old-school basics to what is Today – a fast-changing security landscape.
American Security Today is uniquely focused on the broader Homeland Security & Public Safety marketplace with over 75,000 readers at the Federal, State, and local levels of government as well as firms allied to the government.
American Security Today brings forward a fresh compelling look and read with our customized digital publications that hold readers’ eyes throughout the story with cutting-edge editorial that provides solutions to their challenges.
Harness the Power of the Web – with our 100% Mobile Friendly Publications

AST Digital Publications are distributed to over 75,000 qualified government and homeland security professionals, in federal, state, local, and private security sectors.
‘PROTECTING OUR NATION, ONE CITY AT A TIME’
AST Reaches both Private & Public Experts, essential to meeting these new challenges.
Today’s new generation of public safety and security experts need real-time knowledge to deal with domestic and international terrorism, lone wolf attacks, unprecedented urban violence, shifts in society, culture, and media bias – making it increasingly difficult for Homeland Security, Law Enforcement, First Responders, Military and Private Security Professionals to implement coordinated security measures to ensure national security and improve public safety.
These experts are from Government at the federal, state, and local levels as well as from private firms allied to the government.
AST provides a full plate of topics in our AST Monthly Magazine Editions, AST Website, and AST Daily News Alerts, covering 23 Vital Sectors such as Access Control, Perimeter Protection, Video Surveillance/Analytics, Airport Security, Border Security, CBRNE Detection, Border Security, Ports, Cybersecurity, Networking Security, Encryption, Law Enforcement, First Responders, Campus Security, Security Services, Corporate Facilities, and Emergency Response among others.
AST has Expanded readership into integral Critical Infrastructure audiences such as Protection of Nuclear Facilities, Water Plants & Dams, Bridges & Tunnels, and other potential targets of terrorism.
Other areas of concern include Transportation Hubs, Public Assemblies, Government Facilities, Sporting & Concert Stadiums, our Nation’s Schools & Universities, and Commercial Business Destinations – all enticing targets due to the large number of persons and resources clustered together.
To learn more, please see the 2022 ‘ASTORS’ CHAMPIONS Edition Fully Interactive Magazine – the Best Products of 2022 ‘A Year in Review.’
The Annual CHAMPIONS edition reviews ‘ASTORS’ Award Winning products and programs, highlighting key details on many of the winning firm’s products and services, including video interviews and more.
 The 2022 CHAMPIONS serves as your Go-To Source through the year for ‘The Best of 2022 Products and Services‘ endorsed by American Security Today – and can satisfy your agency’s and/or organization’s most pressing Homeland Security and Public Safety needs.
The 2022 CHAMPIONS serves as your Go-To Source through the year for ‘The Best of 2022 Products and Services‘ endorsed by American Security Today – and can satisfy your agency’s and/or organization’s most pressing Homeland Security and Public Safety needs.
From Physical Security (Access Control, Critical Infrastructure, Perimeter Protection, and Video Surveillance Cameras and Video Management Systems), to IT Security (Cybersecurity, Encryption, Data Storage, Anti-Malware, and Networking Security – to name a few), the 2022 ‘ASTORS’ CHAMPIONS EDITION has what you need to Detect, Delay, Respond to, and Mitigate today’s real-time threats in our constantly evolving security landscape.
It also features guest editorial pieces from some of the security industry’s most respected leaders and recognized firms in the 2022 ‘ASTORS’ Awards Program.
For more information on All Things American Security Today, as well as the 2023 ‘ASTORS’ Awards Program, please contact Michael Madsen, AST Publisher at mmadsen@americansecuritytoday.com.
AST strives to meet a 3 STAR trustworthiness rating, based on the following criteria:
- Provides named sources
- Reported by more than one notable outlet
- Includes supporting video, direct statements, or photos
Subscribe to the AST Daily News Alert Here.
Learn More…
Highlighting CISA & NIST’s Efforts Under EO 14028: Standards & Security




















