
Guest Editorial by Richard Kanadjian, Encrypted USB Business Manager at Kingston Technology
Today, government entities are filling their workplace environments with all sorts of interesting, novel perks in an attempt to keep staff morale high, workers involved, and, as a way to present themselves as a fun, employee-friendly place to work.
Some of these perks involve allowing employees to bring sons and/or daughters, pets, and even outside food for potlucks.
 In a nod to the digital age, other items that many companies allow workers to bring and use on the job fall into the BYOD category – bring your own device.
In a nod to the digital age, other items that many companies allow workers to bring and use on the job fall into the BYOD category – bring your own device.
It is broadly defined as any technology device owned by the employee and to which the employer has given permission to be used on the job.
A partial listing of such devices includes: cameras, mobile devices, tablets, laptops, PCs and USB flash drives.
While the BYOD concept offers varied advantages, each of these devices also present their own special problems and risks.
This article focuses on the cyber security risks of using BYOD unencrypted USB drives, which singlehandedly can negate millions of dollars spent on cyber security, whether intentionally or through carelessness.
BYOD – A Serious Security Risk
Unencrypted USB drives (also commonly known as removable media, flash drives, thumb drives and other terms) pose a major risk.
While they have revolutionized data transport, they have also introduced grave security concerns.
With their extreme portability, USB drives can turn up anywhere – from jacket pockets to parking lots to bad actors – putting governmental data at risk.
With capacities up to 2TB, their tremendous portability and exceptionally easy plug-and-play capability to be connected to various networks through connected systems, USB drives have proven their value to organizations, government agencies and departments of all sizes.
They are used as file-sharing and mobility storage, backup drives and more.
But they are also very susceptible to being lost, breached or misappropriated which leads to the possibility of critical, classified sensitive data landing in the wrong hands.
Considering government workers at every level produce a wide range and reams of information – everything from top-level national security plans to proposed budgets, speeches, pending legislation, meeting minutes, scientific research, sensitive information, secret dossiers, sealed indictments and privileged communications – it’s no wonder the use of USB drives is a major security concern.
Data Protection – Policies for Removable Media
A first step in securing USB drives – whether government issued or employee BYOD – is to have policies and practices in place that deal with protecting data.
Workers must know and follow these policies and practices to avoid loss of data, compromised data, or malicious virus and malware attacks.
Blocking or prohibiting employees from all USB ports may sound like an easy solution but it may also restrict productivity and lower work efficiency.
Similarly, lending drives to employees as a means to move data outside of the network can open said drives to bringing malware back inside the network.
So, how do you deal with the risks without completely forbidding USB-drive usage and forfeiting all of its conveniences?
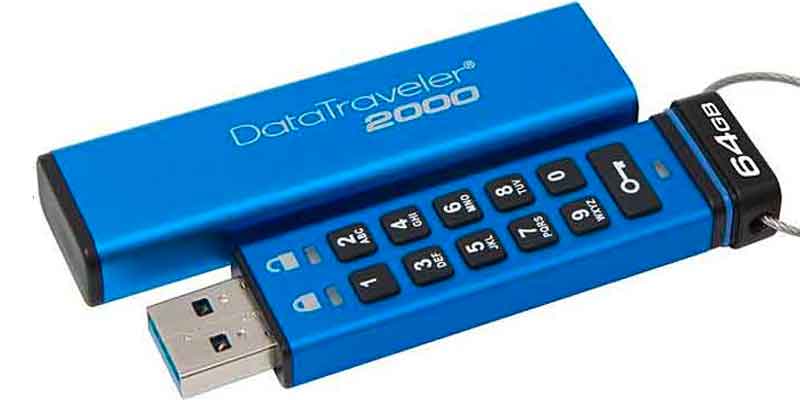
Hardware Encrypted USB drives.
These flash drives are an essential pillar of a comprehensive data loss-prevention (DLP) strategy.
Experts say companies and organizations must insist their employees use only hardware-encrypted USB drives, which combine the productivity advantages of allowing USB access while constantly protecting the information on the drive.
Encrypted USB drives are designed to protect even the most sensitive data, using the strictest security regulations and protocols.
While there are ways to use software encryption to protect data on standard USB drives, these solutions are notoriously hackable and are not recommended for serious security considerations.
The only encryption security for USB drives must be always-on hardware encryption that cannot be defeated; in addition, many of these Encrypted USB drives will offer tamper protection to defend against attacks directed at their internal components.
Encrypted USB drives are powerful tools in closing security gaps and help ensure another layer of security inside and outside the firewall as well as compliance by offering:
-
FIPS Certification – this is how the U.S. Government certifies that these drives do what they are supposed to do and provide different levels of tamper resistance (the most common high-security requirement is FIPS 140-2 Level 3)
-
Latest encryption technology, such as Advanced Encryption Standard (AES) 256-bit encryption in XTS mode
-
Anti-malware / virus protection on board to scan data being copied to the drive
-
Complex password protection to prevent social engineering guessing of passwords.
-
These must be combined with password guessing attacks by limiting the number of wrong passwords entered in a row resulting in a drive reset when the last wrong sequential password is entered
-
-
Ability to be managed remotely, to allow for centralized security management and tracking
-
Tamper evident technology to defend against attacks directed to internal drive components
-
Wide-capacity range to allow from low to high capacities depending upon what is required to mitigate the ability of employees to transfer excessive capacities of data
Encrypted Drives Are The Security Solution
 Encryption of USB drives is performed two ways: either through the device’s hardware or software.
Encryption of USB drives is performed two ways: either through the device’s hardware or software.
The most effective way is through the hardware, as mentioned.
A USB drive with hardware-based encryption is an excellent, non-complicated and simple solution to protect data from breaches, while also providing compliance with evolving governmental regulations.
With flexibility on capacity, they are an ideal solution for applications throughout all levels of government. Such devices meet tough industry security standards and offer the ultimate security in data protection to confidently manage threats and reduce risks.
Governmental agencies such as defense or intelligence and the civilian companies that contract with them, are under intense scrutiny and pressure to comply with a lengthening list of legislative requirements and protocols designed to protect sensitive data in transit and at rest.
A few U.S. legislative requirements include:
-
The Federal Information Security Management Act (FISMA)
-
OMB M06-16 Mandate
-
Federal Desktop Core Configuration (FDCC) mandates
-
Director of Central Intelligence Directive (CDID) 6/3
-
DFARS and NIST – Covered Defense Information (CDI)
Hardware-based encrypted USB drives are self-contained and don’t require a software element on the host computer.
No software vulnerability eliminates the possibility of brute-force, sniffing, and memory hash attacks.

Encrypted drives have digitally signed firmware that cannot be altered as well as a physical layer of protection (this is usually known as protection against BadUSB).
Some of these drives not only come epoxy-dipped, but are epoxy-filled so the casing adds an additional layer of physical security to prevent access to the physical memory.
In contrast, a USB drive with software-based encryption uses software that runs on the host computer and is vulnerable to attacks, and typically does not include the physical layer of security.
Some manufacturers offer free software for encryption but as mentioned earlier, these are not secure solutions that meet the requirements of government data protection.
The top-of-the-line hardware-based encrypted USB drives, such as the Kingston IronKey solutions, use AES 256-bit encryption in XTS mode and are FIPS 140-2 Level 3 certified.
This helps safeguard that anyone who finds such a drive cannot access the information.
(Kingston’s IronKey™ D300 USB Flash drive features an advanced level of security that builds on the features that made IronKey well-respected, to safeguard sensitive information. It’s FIPS 140-2 Level 3 certified, with 256-bit AES hardware-based encryption in XTS mode. An essential pillar to setting security standards, corporate policies and data loss protection (DLP) best practices. An important element in the quest of compliance to industry standards and global regulations such as the GDPR. Courtesy of Kingston Technology and YouTube.)
They also provide brute-force protection as the drive wipes itself clean after 10 attempts of incorrect password guessing.
So, while the drive and its contents are lost, there can be peace of mind that no one else will have the information.
A hardware-centric / software-free encryption approach to data security is the best defense against data loss, as it eliminates the most commonly used attack routes.
This same software-free method also provides comprehensive compatibility with most OS or embedded equipment possessing a USB port.
One way to ensure that only the proper hardware encrypted USB drives are used is to employ DLP software on the network that incorporates endpoint management.

Endpoint management allows security professionals to control which USB devices can be connected to Client devices.
For example, a policy can be set up that limits USB drives to only Kingston IronKey drives which have only been purchased by the government for storage purposes (Kingston offers customizations services to program its encrypted USB drives with unique codes for specific customers).
Other USB drives, including IronKey drives purchased by employees, would be flagged as non-approved and not allowed to attach to the Client nor the network.
Don’t ignore the serious risk of unencrypted BYOD USB drives. Implement a best practices standard and policy and insist all employees – including those that BYOD – only use encrypted USB drives. Keep your data safe.
Kingston Digital, Inc. (KDI), a 2017 ‘ASTORS’ Homeland Security Awards Program Platinum Award Winner for Best Data Storage Security Solution, is the Flash memory affiliate of Kingston Technology Company, Inc., a world leader in memory products and technology solutions.
In 2016, KDI acquired IronKey to become the leader in encrypted USB solutions. IronKey and KDI are headquartered in Fountain Valley, California, USA.
(Encrypted USB Flash Drives keep your private data safe but how do they work? See how and learn ways to make your portable storage safe and secure even if it should accidentally fall into the wrong hands. Whether it be financial papers, personal photos, sensitive work documents or a master plan to take over the world, it’s your private data and you should be able to keep it that way. Courtesy of Kingston Technology and YouTube.)
For more information, please visit www.ironkey.com or www.kingston.com, or call 800-337-8410.
About the Author:
Richard Kanadjian is the Business Manager of Kingston Technology’s Encrypted USB unit.






















