
Guest OpEd by Paul Martini, iboss CEO, CTO, Co-Founder
With increasing bandwidth, encrypted traffic, shifts to cloud applications like Office 365 and users that are no longer constrained to the government network, the ability to deliver fast, secure and compliant connections is more difficult than ever.
A Secure Access Service Edge (SASE) ensures that any connection originating from a user or device to any destination in the cloud is secure and meets government connectivity requirements.
However, with government regulations and security risks associated with SaaS cloud delivered platforms, leveraging a SASE platform for secure connectivity can be a challenge.
The iboss platform is the leading SASE platform that is architecturally based on containerization.
Containerization allows iboss to deliver secure connectivity for users anywhere while maintaining a completely isolated and controlled network data path.
In addition, a fully containerized architecture allows for natural hybrid deployments where proxy and firewall security features can be delivered within the government network, while leveraging the cloud based service, if needed, for remote users.
A SaaS Network Security Service with Containerization at its Core
Understanding containerization is the key for government networks in need of a highly secure service.
With a containerized service like iboss, the network connections from devices and users are processed within isolated containerized gateways which perform proxy and firewall functions.
The containerized gateways never process data for any other organization and data is never mixed with that of any other customer.
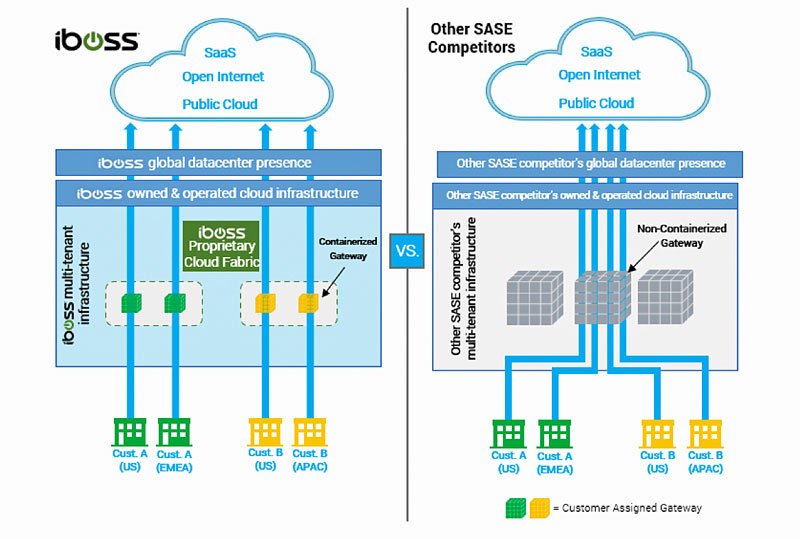
With alternative SASE platforms that lack containerization, network traffic from multiple organizations are processed within the same gateways that proxy, decrypt and firewall data for other organizations.
Mixing data within the gateways that perform functions like decryption not only results in latency but increases security risks.
While Encrypted Traffic Dominates the Cloud, a Containerized Cloud Architecture Makes Inspection of that Traffic More Secure
According to the Google Transparency Report on HTTPS, 99% of all browsing time is over encrypted HTTPS connections.
This requires connections to be decrypted by the SASE service to inspect content for malware, infections and data loss.
To decrypt, special private key files must be used that allow traffic to be inspected and those key files must be available to the cloud gateways performing the inspection.
With a containerized cloud architecture like iboss, full isolation of data is achieved as it moves between users and the cloud, including full isolation of the private keys required to decrypt that traffic.
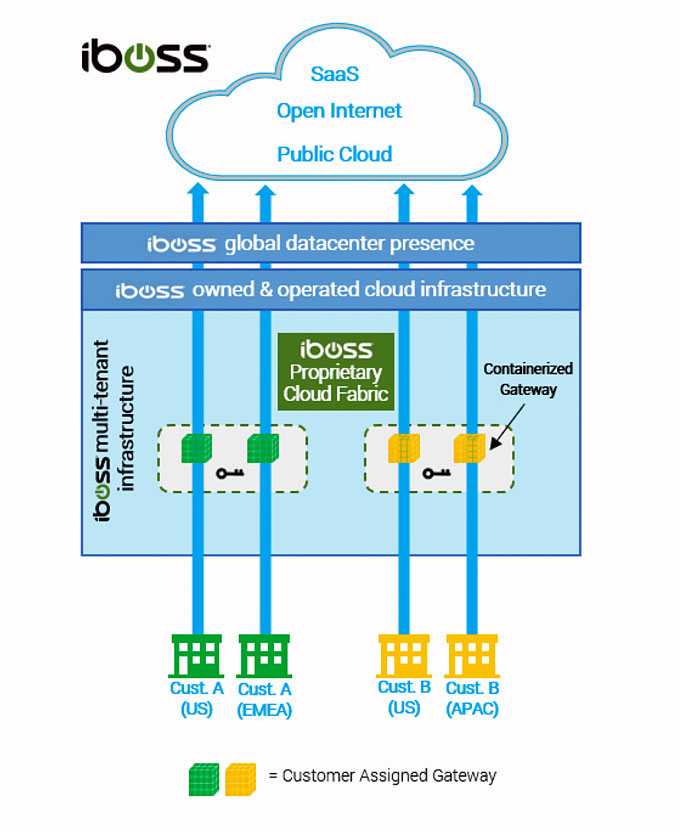
The containerized cloud gateways isolate the private SSL decryption keys to ensure security and reduce risk.
With a non-containerized cloud architecture, the private SSL decryption keys must be made available to the gateways that decrypt network traffic, but those gateways are decrypting and processing traffic for any organization that traverses that gateway.
This poses a big security risk as the decrypted data is now mixed within the proxies and firewalls in the cloud service.
To make things worse, it provides centralized point where all SSL private keys are available so that if a key is compromised for one organization, all keys are compromised for the other organizations that the cloud gateway is servicing.
This has serious implications for high-security organizations, like government agencies.
A SASE Cloud Architecture Designed for Government Comply to Connect Initiatives with Dedicated Source IP Addresses for Users Regardless of Location
Government agencies working on comply to connect initiatives need a predefined set of network security functions applied to connections from users before accessing resources.
This is easier to achieve when users are onsite or within government owned and operated facilities.
As users move outside of the government owned and operated network perimeter, applying needed network security functions to network connections becomes very challenging as the users are connected to untrusted networks, such as their homes or coffee shops, which are outside of the control of the government agency.
Network administrators do not have the advantage of configuring firewalls and routers on networks they do not control.
However, the need to apply a mandatory network security stack to the connections still exists.
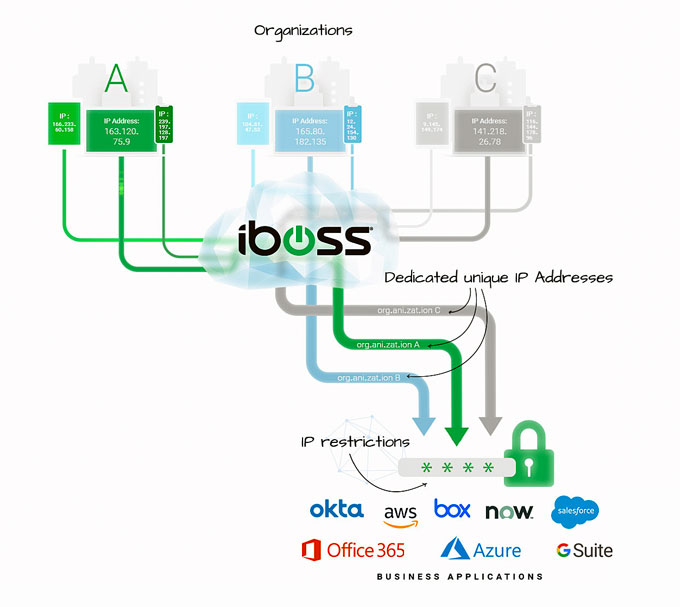
To make things worse, the source IP Address of traffic originating from untrusted, remote networks is random and anonymous making it difficult to access restricted cloud application resources to only trusted IP sources.
The iboss platform provides a consistent network security stack that is applied to users, regardless of their location, including trusted government operated networks and untrusted remote networks.
All traffic originating from users first traverses the iboss cloud platform before making it to its final destination, including public cloud destinations and other destinations like Microsoft Office 365.
And because the iboss platform is a SASE platform that is built on containerization, the source IP Address that is visible to the destination is always dedicated to the government agency.
This means that even if a user is working from a remote network, such as their home, when the network traffic makes it to the application, such as Microsoft Office 365, the source IP Address Office 365 will see is that of the government agency.
(With the COVID-19 pandemic, working from home has brought challenges to organizations as they swiftly adapt to remote work. The limitations and complexity of data backhauling forces many organizations to apply different and often weaker security standards to remote users, leaving them exposed to malware. The solution? The iboss cloud platform can perform any security function that a network firewall or web proxy appliance can perform, without the appliances. The future of network security is here, and it is in the cloud. The iboss cloud provides fast and secure Internet access on any device, from any location, in the cloud. Courtesy of iboss and YouTube. Posted on Apr 15, 2020.)
This has major advantages for government agencies which are running comply to connect initiatives.
First, when a user connects to a cloud application service such as Office 365, the agency can guarantee that the network security policies that specific government agency has in place have been applied.
That is because the source IP Address is only used by users of that specific government agency as the containerized gateways proxy and NAT traffic without mixing data and with the ability to preserve the source IP regardless of user location.
This is unlike a non-containerized model where the source IP Addresses are shared between any customer leveraging the cloud security service.
Although a security policy might be in place, it cannot be guaranteed that it is the network security policy specifically assigned by the government agency.
Additionally, the dedicated and sticky IP Addresses provided by the iboss cloud SASE service allows the government agency to apply login restrictions to cloud applications making originally publicly accessible applications private.
For example, a public cloud application like Microsoft Office 365 can be locked down to only the source IP Addresses that belong to the government agency.
Only users connected through the iboss service, and specifically connected through the agency’s account, will be allowed to connect to the cloud application.

Alternatively, with a non-containerized architecture, any user leveraging the cloud SASE service, regardless of which agency or organization, can connect to the service if IP login restrictions are used.
This is because the IP Addresses between organizations are shared and although you can lock the cloud application down to the ranges belonging to the cloud SASE service, you cannot guarantee the user accessing the front door of the application is that of the specific agency.
Any user running through the SASE service, belonging to any account of the SASE service, can access the application as the entire IP space of the SASE service would have to be used to lock down the cloud application front door.
This also poses challenges in ensuring that the policies in place for comply to connect initiatives are those for the specific government agency.
A Containerized SASE Architecture that is Naturally Hybrid for Government Agencies
A containerized architecture allows the containerized cloud gateways to extend into physical form so they can be run within the government network itself. This includes running the gateways within a government office, base or data center.
The containerized gateways run on physical infrastructure that is within the government network and have the ability to proxy and firewall traffic directly within the government facility without ever sending that traffic through the cloud gateways running within the service.
This is much different than alternative SASE services which are not based on containerization and do not have the ability to naturally extend in the private cloud form.
When the iboss cloud containerized gateways run onsite, within the government network, they can be linked to the global containerized cloud footprint.
This means that traffic from remote users does not have to traverse back to the government datacenter while still having the same network security policies and source IP address ranges in place that are used within the private gateways running within the government facility.
Deployments can be as many private cloud gateways and iboss cloud gateways as needed and can even shift over time.
This provides the flexibility to transition from an on-prem private cloud appliance model to a full SASE model over time and with ease while gaining the benefits of protecting remote workers immediately today.
(Learn More about iboss Cloud Delivered SaaS Network Security. Courtesy of iboss and YouTube. Courtesy of iboss and YouTube. Posted on Feb 27, 2020.)
About the Author

Paul Martini is the CEO, Co-founder and chief architect of iboss.
Prior to founding iboss, Paul was key architect for a wide-variety of complex security and technology solutions for clients such as Phogenix, the U.S. Navy, and Hewlett Packard. He was also a key contributor at Copper Mountain Networks which was a pioneer in introducing broadband networks used by Telcos to build the cloud.
His work at Science Applications International Corporation (SAIC) involved building distributed real-time network systems for companies such as Rolls Royce.
Paul has been recognized for his leadership and innovation, receiving the Ernst & Young Entrepreneur of The Year award and being named one of Goldman Sachs’ 100 Most Intriguing Entrepreneurs.
Paul holds over 190 issued patents in cloud, cybersecurity, networking and technology and has had his work published in many scientific journals, including the Journal of Foundations in Computer Science and the Journal of Analytical Biochemistry.
iboss Named a Finalist in 2020 ‘ASTORS’ Homeland Security Awards Program

The Annual ‘ASTORS’ Awards Program is specifically designed to honor distinguished government and vendor solutions that deliver enhanced value, benefit and intelligence to end users in a variety of government, homeland security and public safety vertical markets.
The Annual ‘ASTORS’ Awards is the preeminent U.S. Homeland Security Awards Program highlighting the most cutting-edge and forward-thinking security solutions coming onto the market today, to ensure our readers have the information they need to stay ahead of the competition, and keep our Nation safe – one facility, street, and city at a time.
90% of ‘ASTORS’ Award Winners return to compete in the Annual ‘ASTORS‘ Homeland Security Awards Program, and 100% of ‘ASTORS’ Sponsors have returned year to year to reap the benefits of their participation in the industry’s largest and most comprehensive Annual Awards Program.

The 2019 ‘ASTORS’ Awards Program surpassed expectations with a record number of nominations received from industry leaders and government agencies, and drew over 200 attendees to the ‘ASTORS’ Awards Presentation Banquet – an exclusive gourmet luncheon and networking opportunity which filled to capacity, before having to turn away late registrants.

The event featured an impassioned and compelling keynote address by William J. Bratton, former police commissioner of the New York Police Department (NYPD) twice, the Boston Police Department (BPD), and former chief of the Los Angeles Police Department (LAPD), as he walked attendees through 50 years of American policing history, the impacts on the communities, and the evolution of critical communication capabilities in our post 9/11 landscape.
Commissioner Bratton, one of the world’s most respected and trusted experts on risk and security issues and Executive Chairman of Teneo Risk a global advisory firm, was recognized as the ‘2019 ‘ASTORS’ Person of the Year’ for his Lifetime of Dedication and Extraordinary Leadership in Homeland Security and Public Safety.
The 2020 ‘ASTORS’ Awards Program is sponsored by ATI Systems, Attivo Networks, Automatic Systems, Desktop Alert, X.Labs and Reed Expositions, every one a returning Sponsor from 2019.
Why the ‘ASTORS’ Homeland Security Awards Program?

American Security Today’s comprehensive Annual Homeland Security Awards Program is organized to recognize the most distinguished vendors of physical, IT, port security, law enforcement, and first responders, in acknowledgment of their outstanding efforts to ‘Keep our Nation Secure, One City at a Time.’
Over 200 distinguished guests representing Federal, State and Local Governments, and Industry Leading Corporate Firms, gathered from across North America, Europe and the Middle East to be honored among their peers in their respective fields which included:
- The Drug Enforcement Administration (DEA)
- National Center for Missing and Exploited Children (NCMEC)
- United States Marine Corps
- The Federal Protective Service (FPS)
- Argonne National Laboratory (ANL)
- United States Postal Inspection Service
- DHS S&T
- United States Marshals Service (USMS)
- The Port Authority of New York & New Jersey Police (PAPD)
- The Department of Justice (DOJ)
- The New York State Division of Homeland Security & Emergency Services (NYS DHSES)
- United States Border Patrol
- AlertMedia, Ameristar Perimeter Security, Attivo Networks, Automatic Systems, Bellevue University, BriefCam, Canon U.S.A., CornellCookson, Drone Aviation, FLIR Systems, Hanwha Techwin, HID Global, IPVideo Corp., Konica Minolta Business Solutions, LenelS2, ManTech, Regroup Mass Notifications, SafeLogic, SolarWinds, Senstar, ShotSpotter, Smiths Detection, TCOM LP, Trackforce, Verint, and More!
From innovative Military Cyber Programs, to Local, State and Federal Public Safety and Emergency Management Initiatives, New Physical and IT Products and Services, and Security Professional, Threat Assessment, Emergency Preparedness, Law Enforcement and Homeland Security Education and Training Opportunities – Join your ‘ASTORS’ Award-Winning Peers and Receive the Recognition You Deserve!
 Excellence in Public Safety and Government Security Award Nominations are also encouraged, such as those 2019 Honored Winners which includes the DEA, U.S. Marine Corps, DHS S&T, Federal Protective Service, DHS S&T NUSTL, U.S. Marshals Service, U.S. Border Patrol, The Port Authority of NY/NJ, and the NYS Division of Homeland Security & Emergency Services.
Excellence in Public Safety and Government Security Award Nominations are also encouraged, such as those 2019 Honored Winners which includes the DEA, U.S. Marine Corps, DHS S&T, Federal Protective Service, DHS S&T NUSTL, U.S. Marshals Service, U.S. Border Patrol, The Port Authority of NY/NJ, and the NYS Division of Homeland Security & Emergency Services.
Why American Security Today?
The traditional security marketplace has long been covered by a host of publications putting forward the old school basics to what is Today – a fast changing security landscape.
The traditional security marketplace has long been covered by a host of publications putting forward the old school basics to what is Today – a fast changing security landscape.
American Security Today is uniquely focused on the broader Homeland Security & Public Safety marketplace with over 75,000 readers at the Federal, State and local levels of government as well as firms allied to government.
American Security Today brings forward a fresh compelling look and read with our customized digital publications that hold readers eyes throughout the story with cutting edge editorial that provides solutions to their challenges.
Harness the Power of the Web – with our 100% Mobile Friendly Publications

The AST Digital Publications is distributed to over 75,000 qualified government and homeland security professionals in federal, state and local levels.
‘PROTECTING OUR NATION, ONE CITY AT A TIME’
AST Reaches both Private & Public Experts, essential to meeting these new challenges.
Today’s new generation of public safety and security experts need real-time knowledge to deal with domestic and international terrorism, lone wolf attacks, unprecedented urban violence, shifts in society, culture and media bias – making it increasingly difficult for Homeland Security, Law Enforcement, First Responders, Military and Private Security Professionals to implement coordinated security measures to ensure national security and improve public safety.
These experts are from Government at the federal, state and local level as well as from private firms allied to government.
AST provides a full plate of topics in our AST Monthly Magazine Editions, AST Website and AST Daily News Alerts, covering 23 Vital Sectors such as Access Control, Perimeter Protection, Video Surveillance/Analytics, Airport Security, Border Security, CBRNE Detection, Border Security, Ports, Cybersecurity, Networking Security, Encryption, Law Enforcement, First Responders, Campus Security, Security Services, Corporate Facilities, and Emergency Response among others.
AST has Expanded readership into integral Critical Infrastructure audiences such as Protection of Nuclear Facilities, Water Plants & Dams, Bridges & Tunnels, and other potential targets of terrorism.
Other areas of concern include Transportation Hubs, Public Assemblies, Government Facilities, Sporting & Concert Stadiums, our Nation’s Schools & Universities, and Commercial Business Destinations – all enticing targets due to the large number of persons and resources clustered together.
To learn more about the 2019 ‘ASTORS’ Homeland Security Award Winners solutions, please go to the 2019 ‘ASTORS’ Championship Edition Fully Interactive Magazine – the Best Products of 2019 ‘A Year in Review’.
The ‘ASTORS’ Champion Edition is published annually and includes a review of the ‘ASTORS’ Award Winning products and programs, highlighting key details on many of the winning firms products and services, includes video interviews and more.
 It is your Go-To source throughout the year for ‘The Best of 2019 Products and Services‘ endorsed by American Security Today, and can satisfy your agency’s and organization’s most pressing Homeland Security and Public Safety needs.
It is your Go-To source throughout the year for ‘The Best of 2019 Products and Services‘ endorsed by American Security Today, and can satisfy your agency’s and organization’s most pressing Homeland Security and Public Safety needs.
From Physical Security (Access Control, Critical Infrastructure, Perimeter Protection and Video Surveillance Cameras and Video Management Systems), to IT Security (Cybersecurity, Encryption, Data Storage, Anti-Malware and Networking Security – Just to name a few), the 2019 ‘ASTORS’ CHAMPIONS EDITION will have what you need to Detect, Delay, Respond to, and Mitgate today’s real-time threats in our constantly evolving security landscape.
It also includes featured guest editorial pieces from some of the security industry’s most respected leaders, and recognized firms in the 2019 ‘ASTORS’ Awards Program.
iboss is a cloud security company that provides organizations secure access to the Internet and their applications on any device, from any location, in the cloud.
The iboss cloud platform provides network security as a service, delivered in the cloud, as a complete SaaS offering, eliminating the need for traditional network security appliances, such as firewalls and web gateway proxies, which are ineffective at protecting a cloud-first and mobile world.
Leveraging a purpose-built cloud architecture backed by over 190 issued and pending patents and more than 100 points of presence globally, iboss protects more than 4,000 organizations worldwide.
To Learn More, please visit iboss or contact the company at info@iboss.com.
For further information on the Annual ‘ASTORS’ Awards Program and advertising opportunities with American Security Today, please contact Michael Madsen, AST Publisher at mmadsen@americansecuritytoday.com.
AST strives to meet a 3 STAR trustworthiness rating, based on the following criteria:
- Provides named sources
- Reported by more than one notable outlet
- Includes supporting video, direct statements, or photos






















