
Guest Editorial by Bharat Bhushan
Microsoft Exchange is a mission-critical e-mail and calendaring server widely used by small businesses, medium organizations, and large enterprises.
It’s a server-side application that runs on Windows Server operating system and stores highly confidential and sensitive business information, such as emails, contacts, attachments, notes, etc.—making it a prime target for attackers.
However, to protect the information, Exchange Server comes with advanced built-in security features, such as:
-
Anti-spam filters for unsolicited junk emails or malicious attachments and links.
-
Secure/Multipurpose Internet Mail Extensions (S/MIME) to allow users to encrypt/decrypt and digitally sign messages and attachments.
-
Kerberos authentication for mailbox access and many more.
However, last year we have witnessed a significant increase in attacks against on-premises Exchange servers mostly targeting small and medium-sized businesses.
Although Microsoft releases regular Security and Cumulative Updates to patch vulnerabilities, thousands of Exchange Servers are still unpatched and vulnerable to malicious attacks.
As a result, multiple state-sponsored and financially motivated cybercriminals are actively looking for vulnerable organizations to exploit Exchange Server vulnerabilities and infiltrate their networks to steal or encrypt their critical data for a ransom.
According to Microsoft, ‘If compromised, Exchange servers provide a unique environment that could allow attackers to perform various tasks using the same built-in tools or scripts that admins use for maintenance.”
In this article, we’ll be sharing some useful tips and solutions to help you deal with various Exchange Server security challenges, protect the information and stay compliant.
Tips to Deal with Exchange Server Security Challenges
Attackers use two types of tactics to bypass Exchange Server security and compromise the server.
-
Social engineering or phishing attacks to steal credentials and infiltrate the network with lateral movements until access to Exchange Server is achieved.
-
Attackers target Exchange Servers with Remote Code Execution (RCE) vulnerabilities. They exploit the vulnerabilities to gain access to the server, deploy web shells, backdoors, and malware.
Below are a few tips and best practices that can help you deal with Exchange Server security challenges and secure your Exchange server from various malicious attacks and threats.
Update Exchange Server
Cybercriminals and threat actors find it easier to penetrate and compromise a vulnerable or unpatched Exchange server. If your server is not patched with the latest Security or Cumulative Updates, attackers may easily compromise your server, enter your organization’s network and put your business data at risk.
You should also keep the Windows Server operating system and other third-party software or add-ins (extensions) updated to patch backdoors and vulnerabilities.
Pro Tip: To find issues with the servers and check overall server health, run HealthChecker.ps1 PowerShell script on Exchange Server. It helps detect common configuration issues and vulnerabilities that you need to patch. It generates a detailed HTML report with recommendations to fix issues with the server to ensure consistent performance and strengthen security.
Deploy Firewalls
Using a firewall is critical to monitor incoming/outgoing traffic and protect the server from threats, such as viruses, malware, worms, etc.
By default, Microsoft Exchange Server relies on Windows Firewall. It adds rules to the firewall for the server to work.
However, you may also manually enter rules to allow or block traffic. If you need more features or control, you may install and use a third-party Exchange-aware firewall app to safeguard the server from malicious attacks and threats.
But never turn off the default Windows firewall. If you need to, make sure the server isn’t exposed to the internet. You may also implement a network firewall for added security.
Password Policy
One of the primary ways to enter an organization’s network is to steal user credentials. Thus, it’s critical to implement a strict password policy defining following,
-
Users must use a unique and complex password created using a combination of letters (with at least 1 uppercase/lowercase letter), numbers, and special characters.
-
Users must change their passwords after a specific timeframe, such as every 45 days or so. Implementing the shortest timeframe is recommended.
-
Users cannot reuse their old passwords.
Train Employees and Users
If you want to prevent attackers from stealing user passwords, it is important to educate and train your users and employees to identify spam or phishing emails.
Additionally, add a group policy to prevent users from opening a hyperlink directly from their email client app or other Office documents. This will help prevent users from opening a malicious link or downloading an infected document or malware on their system.
You may also add a banner or warning message to flag the emails incoming from outside your organization.
Multi-Factor Authentication (MFA)
Multi-Factor Authentication using an authenticator app or OTP via SMS can help you further fortify the Exchange Server security. By implementing and necessitating multifactor authentication, you can prevent threat actors from accessing the server or mailboxes even if they have stolen the password via social engineering or phishing attacks.
This will safeguard your organization from attackers accessing user mailboxes and entering your organization’s network even if users are reusing the same passwords for other websites or using weak passwords to login into their accounts.
Backup Policy
Backups are critical as they come in handy when the server gets damaged or compromised after an attack. It also helps you restore user mailboxes if the database gets damaged due to server crashes, abrupt shutdown, or hardware/software failure.
Use Windows Server Backup service in Exchange Server to create Volume Shadow Copy Service or VSS-based backups. You may also use any third-party Exchange-aware backup utility for regular backups. Besides creating backups, it’s also critical to test and label them correctly to ensure they will work when needed.
Besides backup, you should also keep an Exchange server recovery software, such as Stellar Repair for Exchange, handy. It helps you restore mailboxes and mail items created between the backups.
Moreover, it can help when the backup doesn’t work, gets damaged, or fails to restore data when required.
To Wrap Up
Continuous attacks on on-premises Exchange Server over the last year have highlighted the importance of other aspects of Exchange Server security.
Although Microsoft releases regular updates to patch vulnerabilities, it’s not always possible to patch the server immediately and may require some additional time to complete the process.
In this article, we discussed tips and best practices that you may follow to overcome such Exchange Server security challenges and fortify the server.
About the Editor

Bharat Bhushan is an experienced technical Marketer working at Stellar Data Recovery – expertise in data care. He is skilled in Microsoft Exchange Database, MSSQL Database troubleshooting & data warehousing.
Bhushan is also a Management Post Graduate, has a strong grip in Technology, and is certified in SAP-SD, Oracle 10g & Informatica Powercenter 9.1.
Related Technologies…
Canon Recognized for Best Email Security Solution in 2021 ‘ASTORS’ Awards Program

American Security Today’s Annual ‘ASTORS’ Awards is the preeminent U.S. Homeland Security Awards Program, and now entering its Seventh Year, continues to recognize industry leaders of Physical and Border Security, Cybersecurity, Emergency Preparedness – Management and Response, Law Enforcement, First Responders, as well as federal, state and municipal government agencies in the acknowledgment of their outstanding efforts to Keep our Nation Secure.
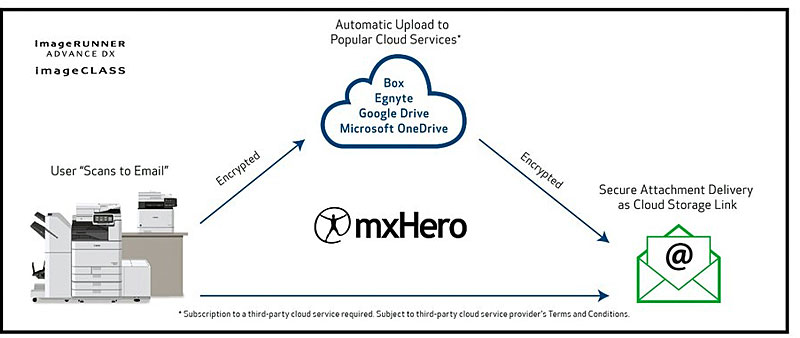
Canon U.S.A. (First of Two)
Best Email Security Solution
-
mxHero + Canon MFP
-
A cloud service for intelligent email management, mxHero™, can integrate onto a Canon multifunction printer (MFP) to help customers safely collaborate, govern, manage and share information.
-
By leveraging powerful storage platforms like Box (purchased separately), it can help create a cost-effective solution superior to single-purpose, document/email management products by replacing inbound and outbound email attachments with secure file links.
-
This solution is made to be compatible with most devices, helps to minimize end user effort, provides security measures to help control access to attachments (even when outside of the company) and can help screen malicious content.
-
Especially in today’s environment where solutions designed to help team’s collaborate while working in multiple places is important, services such as mxHero™ can help companies implement security features, govern and manage attachments while people aren’t able to physically connect face-to-face.
Canon U.S.A. (Second of Two)
Best IT Access Control & Authentication System
-
imageRUNNER ADVANCE DX Series + uniFLOW Online + Print via Cloud
-
The latest edition of the imageRUNNER ADVANCE platform, the imageRUNNER ADVANCE DX series with uniFLOW Online, is designed to help prepare its customers for the future of work through its simple, flexible design, advanced scanning, strong security, enhanced cloud features and user-friendly enhancements, like soft number keys similar to a smartphone or tablet.
-
The uniFLOW/uniFLOW Online platform is an end-to-end device management solution that can help improve the control and efficiency of imageRUNNER ADVANCE and other compatible multifunction print solutions through its security features.

-
The platform provides business employees the ability to control and monitor access to sensitive information with its enhanced authentication and user tracking features.
-
To help limit unauthorized use of devices and keep valuable and confident information safe, uniFLOW requires users to identify themselves at the solution, and its Secure Print functionality allows users to send sensitive documents to compatible network printers from desktops and compatible mobile devices.
-
When using this function, regardless of how users submit a print job, documents only print when the user is physically standing at the device and authenticates.
-
Through uniFLOW Online’s ability to store print jobs and release them only when users are in front of the supported Canon print device, solutions such as this help to limit document contamination, which is especially important in our current environment where mitigating contact between individuals is vital.
(Having the needs of the end-user in mind, we started to create a brand-new device user interface (UI) for uniFLOW Online. With a modern look and feel, uniFLOW Online focuses primarily on the login process on Canon imageRUNNER ADVANCE DX devices. It introduces the possibility of adapting the UI to suit customers’ own corporate identity. Subsequent development will expand the optimized user experience to secure printing and scanning functionalities. Courtesy of uniFLOW and YouTube.)
-
*Canon U.S.A. was also recognized with Multi-Award Wins in the 2020, 2019, 2018 and 2017 ‘ASTORS’ Awards Programs.
-
Additionally, Axis Communications, a Canon Company has been recognized in the 2020, 2019, 2018 and 2017 ‘ASTORS’ Awards Programs respectively.
The Annual ‘ASTORS’ Awards highlight the most cutting-edge and forward-thinking security solutions coming onto the market today, to ensure our readers have the information they need to stay ahead of the competition and keep our Nation safe – one facility, street, and city at a time.

AST Honors Thomas Richardson, FDNY Chief of Department; Dr. Kathleen Kiernan, President of NEC National Security Systems; and Richard Blatus, FDNY Assistant Chief of Operations, at the 2021 ‘ASTORS’ Awards Luncheon at ISC East.
The United States was forever changed 20 years ago on September 11th, and we were fortunate to have many of those who responded to those horrific tragedies join us at the 2021 ‘ASTORS’ Awards Luncheon.
In the days that followed 9/11, the critical needs of protecting our country catapulted us into new and innovative ways to secure our homeland – which is how many of the agencies and enterprise organizations that are today ‘ASTORS’ Awards Champions, came into being.

Our keynote speaker featured a moving and informative address from TSA Administrator and Vice-Admiral of the United States Coast Guard (Ret), David Pekoske; to our attendees who traveled from across the United States and abroad, on the strategic priorities of the 64,000 member TSA workforce in securing the transportation system, enabling safe, and in many cases, contactless travel.
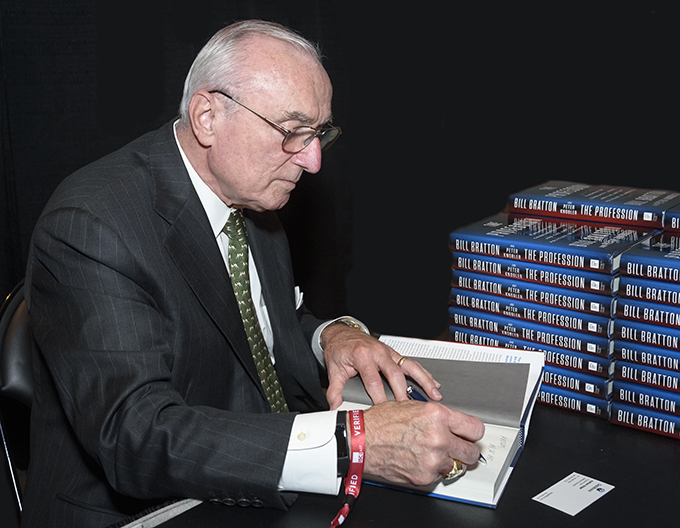
Legendary Police Commissioner William Bratton of the New York Police Department, the Boston Police Department, and former Chief of the Los Angeles Police Department was also live at the event, meeting with attendees and signing copies of his latest work ‘The Profession: A Memoir of Community, Race, and the Arc of Policing in America,’ courtesy of the generosity of our 2021 ‘ASTORS’ Awards Premier Sponsors.
The 2021 ‘ASTORS’ Awards Program was Proudly Sponsored by AMAROK, Fortior Solutions and SIMS Software, along with Returning Premier Sponsors ATI Systems, Attivo Networks, Automatic Systems, and Reed Exhibitions.
Why American Security Today?
The traditional security marketplace has long been covered by a host of publications putting forward the old school basics to what is Today – a fast-changing security landscape.
American Security Today is uniquely focused on the broader Homeland Security & Public Safety marketplace with over 75,000 readers at the Federal, State, and local levels of government as well as firms allied to the government.
American Security Today brings forward a fresh compelling look and read with our customized digital publications that hold readers’ eyes throughout the story with cutting-edge editorial that provides solutions to their challenges.
Harness the Power of the Web – with our 100% Mobile Friendly Publications

AST Digital Publications are distributed to over 75,000 qualified government and homeland security professionals, in federal, state, local, and private security sectors.
‘PROTECTING OUR NATION, ONE CITY AT A TIME’
AST Reaches both Private & Public Experts, essential to meeting these new challenges.
Today’s new generation of public safety and security experts need real-time knowledge to deal with domestic and international terrorism, lone wolf attacks, unprecedented urban violence, shifts in society, culture, and media bias – making it increasingly difficult for Homeland Security, Law Enforcement, First Responders, Military and Private Security Professionals to implement coordinated security measures to ensure national security and improve public safety.
These experts are from Government at the federal, state, and local level as well as from private firms allied to the government.
AST provides a full plate of topics in our AST Monthly Magazine Editions, AST Website, and AST Daily News Alerts, covering 23 Vital Sectors such as Access Control, Perimeter Protection, Video Surveillance/Analytics, Airport Security, Border Security, CBRNE Detection, Border Security, Ports, Cybersecurity, Networking Security, Encryption, Law Enforcement, First Responders, Campus Security, Security Services, Corporate Facilities, and Emergency Response among others.
AST has Expanded readership into integral Critical Infrastructure audiences such as Protection of Nuclear Facilities, Water Plants & Dams, Bridges & Tunnels, and other potential targets of terrorism.
Other areas of concern include Transportation Hubs, Public Assemblies, Government Facilities, Sporting & Concert Stadiums, our Nation’s Schools & Universities, and Commercial Business Destinations – all enticing targets due to the large number of persons and resources clustered together.
(See just a few highlights of American Security Today’s 2021 ‘ASTORS’ Awards Presentation Luncheon at ISC East. Courtesy of My Pristine Images and Vimeo.)
To learn more about ‘ASTORS’ Homeland Security Award Winners solutions, be on the lookout for the 2021 ‘ASTORS’ CHAMPIONS Edition Fully Interactive Magazine – the Best Products of 2021 ‘A Year in Review’.
The Annual CHAMPIONS edition includes a review of Annual ‘ASTORS’ Award Winning products and programs, highlighting key details on many of the winning firm’s products and services, including video interviews and more.

It will serve as your Go-To Source throughout the year for ‘The Best of 2021 Products and Services‘ endorsed by American Security Today, and can satisfy your agency’s and/or organization’s most pressing Homeland Security and Public Safety needs.
From Physical Security (Access Control, Critical Infrastructure, Perimeter Protection, and Video Surveillance Cameras and Video Management Systems), to IT Security (Cybersecurity, Encryption, Data Storage, Anti-Malware and Networking Security – Just to name a few), the 2021 ‘ASTORS’ CHAMPIONS EDITION will have what you need to Detect, Delay, Respond to, and Mitigate today’s real-time threats in our constantly evolving security landscape.
It will also include featured guest editorial pieces from some of the security industry’s most respected leaders, and recognized firms in the 2021 ‘ASTORS’ Awards Program.
-
For a complete list of 2021 ‘ASTORS’ Award Winners, begin HERE.
For more information on All Things American Security Today, as well as the 2021 ‘ASTORS’ Awards Program, please contact Michael Madsen, AST Publisher at mmadsen@americansecuritytoday.com.
AST strives to meet a 3 STAR trustworthiness rating, based on the following criteria:
- Provides named sources
- Reported by more than one notable outlet
- Includes supporting video, direct statements, or photos






















