
Guest OpEd by Mike Wood, CMO, Versa Networks
Government organizations, like many large enterprises, are experiencing significant changes in how users expect and need to access information and services.
Government organizations are adopting new service delivery models, resulting in what is called the ‘modernization of government’.
This change in government IT is taking place during increasingly sophisticated cyber threats and a dramatic expansion of the government’s cyber defense operations.
Three forces – changing user expectations, changing service delivery models, and increasing cyber threats – combine in challenging ways as users move to more remote and mobile access.
IT services are evolving to a multi-cloud model with critical and sensitive services spread across traditional data centers, on-prem clouds and commercial clouds.
With this changing landscape, there is an urgent need to upgrade network security architectures to provide cyber defenders with the enhanced capabilities needed for assigned missions.
The Department of Defense (DoD) and the government’s many Civilian Agencies have similar, but slightly different approaches to providing network security.
The DoD builds a security architecture that aligns with organizational cyber defense roles and responsibilities, providing a robust set of capabilities for each cyber defense organization.
At a very high level, the DoD builds cyber defenses into every critical boundary position. Security policies and sensor data are aligned with the organization’s responsibility for defending each portion of the network.
In several cases, a single network boundary will have responsibilities assigned to multiple sub-organizations resulting in layers of duplicative capabilities so that each sub-organization has capabilities under their control.
For example, at the military installation boundary, the DoD has established a set of capabilities within the Joint Regional Security Stacks (JRSS) that are used by the Military Service that owns the installation and a second set of capabilities that support the Defense Information System Agency (DISA)’s mission to defend the DoD enterprise.
(The Joint Regional Security Stacks (JRSS) includes a suite of equipment that performs firewall functions, intrusion detection and prevention, enterprise management, and virtual routing and forwarding, as well as other network security capabilities. Courtesy of USDISA and YouTube.)
Civilian Agencies address network security requirements primarily through the Trusted Internet Connection (TIC) program.
Enterprise level capabilities are implemented at all of an agency’s connections to the internet and essentially create a trusted zone connected to an untrusted (internet) zone.
TIC 3 moves in a direction similar to the DoD with multiple Policy Enforcement Points tailored to the technical requirements and risk posture of each individual agency component or service provider.
(Learn More about Trusted Internet Connection (TIC) 3.0 which expands on the Cybersecurity and Infrastructure Security Office’s original TIC initiative to provide flexible guidance for better securing a wide spectrum of agency network architectures. Addressing demand for a less prescriptive approach, TIC 3.0 recognizes shifts in modern cybersecurity and advances in technology to guide agencies toward desired outcomes. Courtesy of F5 DevCentral and YouTube. Posted on Jan 13, 2021.)
In both the DoD and Civilian Agency models, the government supports the change in user access and service delivery by creating some forced network flows (backhaul) and by building some additional boundaries for things like cloud access that provide a secure boundary connecting DoD or Civilian Agency networks with commercial clouds and mobility gateways.
This traditional approach does provide cyber defenders with the capabilities and visibility they need while modernizing to mobile and multi-cloud services, but slows the path to modernization and introduces operational inefficiencies, high costs and risks.
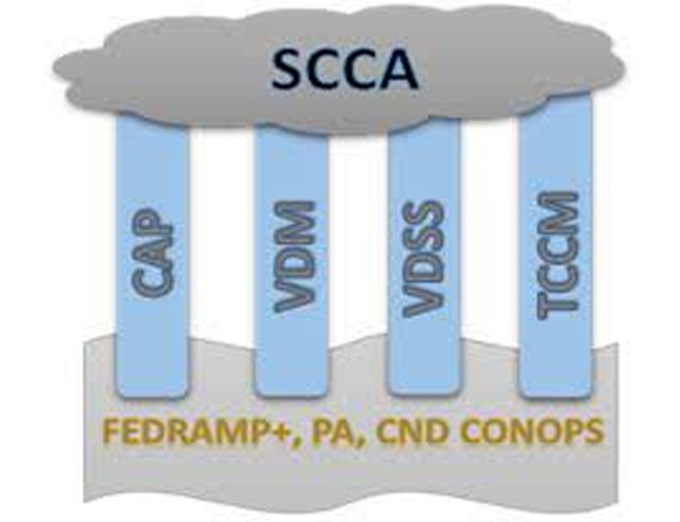
A good example of how the DoD adapts to the challenges of supporting cloud migrations while meeting the cyber defender’s requirements is in the Secure Cloud Computing Architecture (SCCA) developed by the DISA.
The SCCA provides a set of functional requirements for cloud access points and shows how they align to the DoD’s cyber defense organizations.
Challenges to implementing comprehensive client-to-cloud security solutions, arise as government agencies transition to multi-cloud environments and need to deliver increasing support to remote employees.
Key attributes of traditional approaches that inhibit IT modernization and drive up costs include the following:
-
Frequent reconfiguration: It is time-consuming and complicated to re-configure every time a security change needs to be made to mirror the fast-changing threat environment
-
Lack of integrated tools: Organizations lack integrated tools and real-time network analytics to efficiently secure the modern-day network
-
Limits of physical site operations: Operations are anchored to physical sites
-
Multiple software stack inefficiencies and vulnerabilities: Modernization requires multiple software stacks which introduce additional security vulnerabilities
-
High skill demands on operators: Operators and cyber defender organizations require their IT staff to be skilled in many different vendor-specific interfaces
-
In addition to supporting and enabling a wide range of government modernization efforts, there is a need to address some related challenges with the traditional approach to delivering cyber defense capabilities:
-
Network Traffic Bottlenecks: Traditional architectures create performance impacts by forcing traffic through multiple, often duplicate, systems and capabilities in order to apply the policies of multiple organizations. This creates bottlenecks when there are major changes to service delivery (e.g. the introduction of cloud migrations).
-
High Operations and Maintenance (O&M) Costs: Traditional approaches drive up the cost of provisioning, maintaining and enhancing the security architecture as organizations deploy new capabilities to support IT modernization objectives.
-
Innovation Speed Bumps: Today’s security architectures often slow introduction of new innovations as they are anchored to physical sites and are unable to scale up or down as needed.
What is SASE and how does it support Government Modernization?
Secure Access Service Edge, or SASE, creates a secure bridge between access and the service edge (the cloud, data center, corporate network, internet). SASE predicates access on the identity of an individual, device, application, or service.
Simply put, the goal of SASE is to provide secure Work-from-Anywhere (WFA) user access to all applications and data, no matter where the user is located.
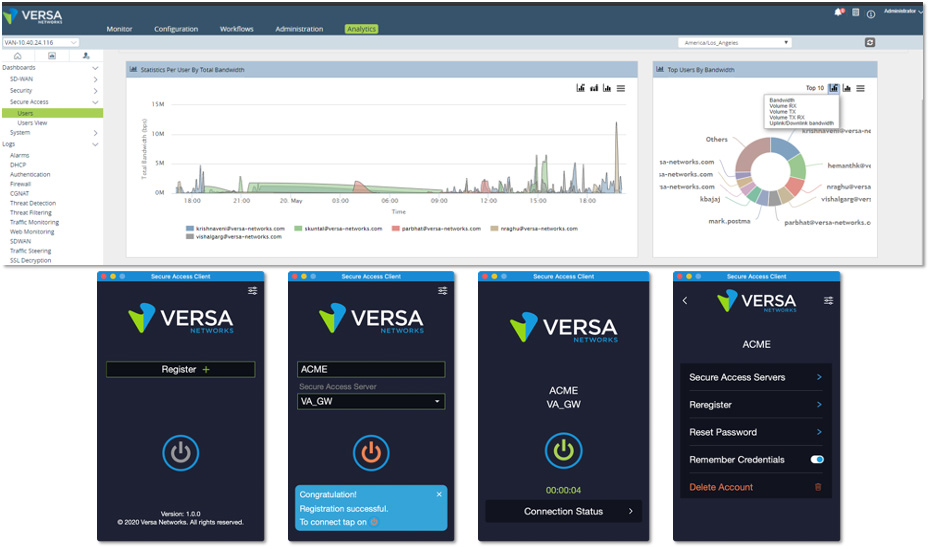
It combines SD-WAN and network security functionality via the cloud so that enterprises can manage security at the edge more effectively.
(Learn More. Visit https://versa-networks.com/ or request to speak with an engineer: https://versa-networks.com/demo/. Courtesy of Versa Networks.)
SASE is a change to how and where security is applied and supports all of the features usually available in more traditional security architectures.
The potential for SASE controls is bounded only by the state of the art in cyber defenses.
While SASE is new, it exists in production and supports large enterprises today – it isn’t just hype, marketing and slide-ware.
The potential for leveraging SASE is demonstrated by the array of deployment options (on-premises, via the cloud, or both) currently available from SASE industry leaders.
Deploying SASE solutions helps customers:
-
Deliver optimal user experience
-
Mitigate network vulnerabilities
-
Increase security, and
-
Reduce IT complexity and costs through a single service
SASE is composed of five main technologies:
-
SD-WAN
-
Firewall as a service (FWaaS)
-
Cloud Access Security Broker (CASB)
-
Secure Web Gateway (SWG), and
-
Zero-Trust Network Access (ZTNA
SASE shifts away from a traffic flow model where traffic is forced to a specific policy enforcement point to get the appropriate controls.
Instead, it is structured around an architecture where capabilities are “ubiquitous” and controls are applied based on user identity and context.
Capabilities are ubiquitous in the sense that they are provisioned in software at points supporting efficient access, either as Software as a Service (SaaS) in the cloud or in more traditional on-prem capabilities.
The key to the SASE approach is that all the policies are applied via a single pass through the optimal SASE access point.
This, coupled with the elimination of backhaul, significantly improves performance and reduces cost while still delivering the capabilities, control, and visibility required by government cyber defenders.
About the Author
 Michael Wood leads the Versa Networks marketing organization and drives brand awareness, messaging, positioning, product marketing, demand generation, analyst engagements, press relations and corporate communications.
Michael Wood leads the Versa Networks marketing organization and drives brand awareness, messaging, positioning, product marketing, demand generation, analyst engagements, press relations and corporate communications.
He is an industry veteran with 30 years of experience in marketing, product and engineering at companies such as StrataCom, Cisco, Akamai, VeloCloud, VMware and Apstra.
Mike holds a Master of Science degree in Electrical Engineering and a Bachelor of Science degree in Industrial Technology (Computer Electronics) from San Jose State University.
AST strives to meet a 3 STAR trustworthiness rating, based on the following criteria:
- Provides named sources
- Reported by more than one notable outlet
- Includes supporting video, direct statements, or photos
Subscribe to the AST Daily News Alert Here.
Related Technologies…
New TSA Cybersecurity REQs for Critical Pipeline Owners/Operators

















