
By Kayleigh Alexandra
For well over a decade, remote working was an option that most businesses left in their back pockets.
They knew it to be technically viable, and accepted some of the noted benefits, but were broadly reluctant to leave the traditional office structure.
Allow people to work remotely, they feared, and they’d shirk their responsibilities — getting paid to do relatively little.
And while it was steadily gaining traction as the years went by, with enough open-minded companies adopting it and ultimately demonstrating that it could work effectively, this reluctance remained common.

The average business was afraid to give up the office space it so clearly associated with industry credibility, and resolved to deny remote working for as long as possible.
Then along came the COVID-19 pandemic to take lives, destabilize economies, and change the world of business forever.
With much of the globe in lockdown, most companies that were able to continue had to start operating remotely most or all of the time — and though many weren’t prepared, they leaned on the SaaS world and managed to get by.
Now that some months have passed, most businesses seem to have adapted well enough that they’d consider continuing to work remotely when things mostly return to normal: but is that a good idea?
Leaving aside productivity and convenience, there’s the significant matter of security.
Is remote working secure enough to be the new standard? Let’s consider it.
Exceptional security is available, but it comes at a cost
Just as you can assemble a highly-skilled team of security guards to prevent anyone from getting into a physical space, you can lean on sophisticated software to secure an online system, but it will cost you.

Most people don’t like the idea of paying for virtual security: paying for locks is one thing (you can hardly download a lock), but shouldn’t online systems be secure by default and not require any additional attention?
And sure, there are some things you can do that won’t cost you extra. You can keep each computer shielded from malware using free services (Spybot – Search & Destroy is still free for private use, making it viable for freelancers), so you don’t necessarily require anything to keep your machine working well.
You can also protect your private data to some extent by using a free VPN (this guide by What’s My IP points out some options), though with limited functionality.
Overall, though, if you want professional-level protection — particularly for business data — then you’re going to need to pay for an enterprise solution of some kind (usually a cloud solution from a provider such as Microsoft).
This can get fairly costly for a large organization. You do, of course, need to factor in the money saved from not having a standard office.
The baseline isn’t worse than office security
What if you do nothing at all to protect your data while working remotely?
How likely are you to fall victim to a criminal act, or see any of your data lost through an accident?
Well, to be fair, we need to compare this scenario to working in a regular office with no paid security.
Working remotely, you can forget your authentication details (particularly when using multi-factor authentication), send a link to the wrong person, click on an ad for something fake, have your online activity traced, or even see your laptop or smartphone stolen.
Working in an office, though, all of those things can still happen to you: the consequences are just dissimilar.
If you forget your authentication details in the office, your IT lead can help you recover access, so that’s an advantage — but if an infection slips through your protection, it might be able to get into the intranet, potentially damaging many other machines.
Keeping things in an office will make them safer, but it will also make them more likely to be targets for people who’d actually be interested in the data (instead of just wiping and selling the hardware).
Worker training is possibly the biggest obstacle
So far, we’ve seen that remote working security isn’t actually all that dissimilar from conventional security.

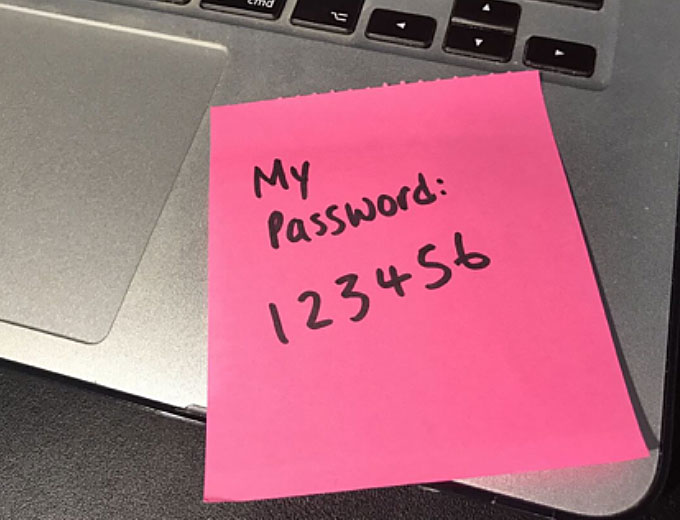
If you want your system to be secure, you need to pay for it, and if you’re sloppy with your security then you’re going to be in trouble.
Does this mean that you’re no safer in an office than working remotely, then?
Well… not quite.
The differentiating factor is the difficulty of training.
When you have everyone working in an office, you can have the IT department set everything up and establish shields to prevent those who aren’t overly tech-savvy from causing problems (stopping them from accessing certain sites, for instance, or launching certain applications).
Training isn’t all that important.
For remote workers, though, training is very important.
If something confuses one of your employees, you can’t just have someone go to their desk to help them out — and this lack of control (coupled with the difficulty of keeping restrictions on machines you let your workers take away with them) can lead to major mistakes being made.
Is remote working as secure as it needs to be, then?

















